Passwordless authentication is here

Passwords suck! There, I said it. We've all heard it said many times before, but it’s worth repeating. The concept of gate-keeping access to digital services with a username and password may have been appropriate, and even good practice, in the early days of computing when a person might only have one or two logins to maintain. However, in today’s world where people have hundreds of accounts, they tend to re-use one password for multiple accounts or outsource the job to a password manager service. And even if you do manage to create a complex and unique password for each account, and remember it at the time of login, there is still the problem of data breaches, which are becoming all too common.
To better understand the problem, let’s break down what a password is: it’s “something you know”, but because it’s a shared secret that gets used multiple times, it’s more specifically called a static knowledge-based authentication credential.
There are two other main authentication categories: possession, (something you have) and inherence (something you are).

All authentication is based on the premise that when you can claim an identity, by providing a username, and back up that claim with at least one type of authentication, you should be granted access. So, if we want a viable passwordless future, we need to leverage other forms of authentication.
The role of biometrics in strong customer authentication
The good news is that there are other ways we can achieve this, several of which are already commonplace. A great example is how we almost never unlock smartphones using the device PIN, but gain access using biometrics – originally with fingerprint technology and more recently with facial recognition.
The example shows that it’s possible to swap one type of authentication for another to improve security and user experience. However, we can also combine multiple authentication types – one of which, ideally, should be communicated through an out-of-band channel – for even greater security.
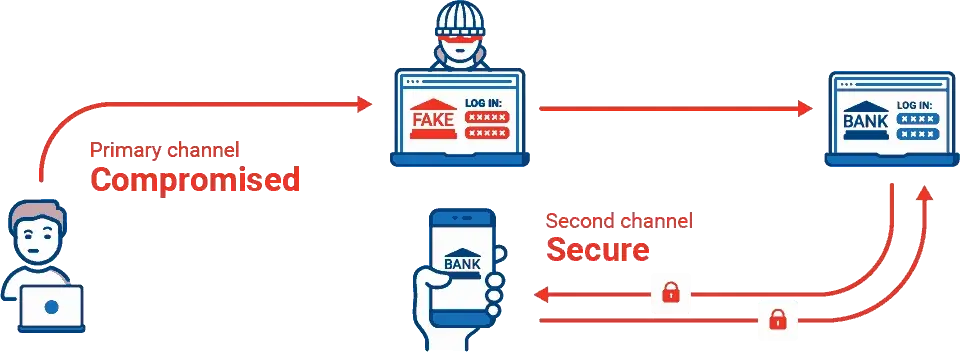
The practice of combining two or more factors is called two-factor or multi-factor authentication. The premise here is that if I can prove I have more than one of the devices or channels linked to an identity, it further increases the strength of my authentication claim.
Find out how FIDO tokens are paving the way to a more secure, passwordless future. Download our latest ebook, The ultimate guide to FIDO.
The login experience that many of us have already incorporated into the way we use our smartphones should be replicated across more use cases, although we are seeing this start to happen as many industry leaders begin to align themselves to an international standard called FIDO (Fast ID Online). This standard aims to make passwords obsolete by replacing them with possession and biometric factors. It also uses encryption technology to ensure that your credentials cannot be stolen.
With several tech giants – Google, Apple and Microsoft to name a few – now supporting this standard, it may well be the solution that finally allows us to remove passwords from our lives for good.







